Aim
This task aims to assess your understanding of cryptography concepts, and encryption techniques, creativity and problem-solving skills, and collaboration skills with your partner.
Your task is to create a cryptography puzzle that consists of at least 3 layers of security. Your puzzle should use a range of cryptography techniques including one of the cipher methods we learned in class.
How it will be Assessed
Your puzzle will be graded according to the following criteria:
- Collaboration & contribution skills.
- Creativity and complexity.
- Understanding & implementation of Encryption techniques.
- Clarity of instructions & hints
- Presentation & peer engagement to the testing of others puzzles.
The rubric for this task can be found here:
Instructions
Follow the steps below carefully to complete the task.
Step 1: Research, inspiration and ideas.
Conduct research based on encryption methods we have covered in class, as well as additional ideas you may be able to use to help create your puzzle.
Record a list of your ideas on a Word Document.
Step 2: Make your puzzle.
Begin the process of creating your puzzle. Establish what will happen in each layer of security and encryption.
(Feel free to collect resources and materials or make your own in this stage.)
Begin making your clues, hints or steps required to complete your puzzle. Ensure these are presented in a way for someone to follow.
Step 3: Testing your puzzle.
Test your own puzzle to ensure it works. If there are any changes or amendments to be completed, ensure they are corrected before final submission and presentation.
Step 4: Presenting your puzzle.
Discuss the best way to present your puzzle to the group with me and gather any resources needed to do so.
You will have half a lesson to present your puzzle to the group as well as take part in the completion of other groups puzzles.
Example Puzzle Ideas:
Use the ideas below to help your get started:
Substitution Cipher Puzzle:
Encrypt a short message using a simple substitution cipher (e.g., A=1, B=2) and provide a key for reference.
Include hints like “The alphabet has been shifted by 3 positions.”
Transposition Cipher Puzzle:
Rearrange the letters of a sentence using a transposition cipher and provide a clue on the rearrangement pattern.
Offer a hint like “Read every third letter in reverse.”
Caesar Cipher Puzzle:
Encrypt a famous quote using a Caesar cipher with a specific shift value.
Provide a hint that indicates the shift value, but not the plaintext.
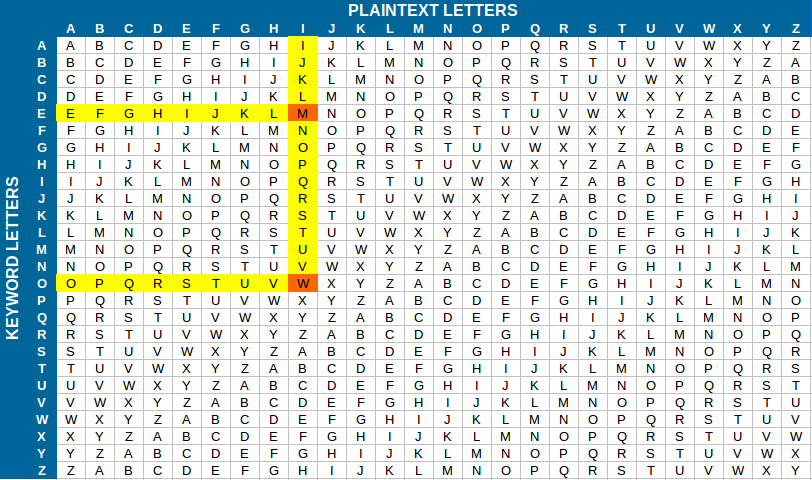
Vigenère Cipher Puzzle:
Develop a Vigenère cipher puzzle and provide a keyword.
Challenge your peers to decipher the message with the given keyword.
Hints and Tips:
- Think outside the box!
- Incorporate basic puzzles like dot-to-dots, crossword puzzles or find-a-words into your puzzle to add layers of complexity.
- Revisit past grok modules, How do they create puzzles?